Just last week, my nephew, a Gen Z native, sent me a simple text: "On my way." That innocuous four-word message, like the estimated 350 billion messages exchanged daily worldwide, vanished from his phone and appeared on mine almost instantly. We live in an era where communication feels effortless, instantaneous, almost magical. But beneath that seamless experience lies an intricate, global symphony of hardware, software, and complex protocols working in perfect, coordinated harmony. What happens behind the scenes when you send a message online isn't just about speed; it's about an invisible ballet of data packets traversing vast distances, protected by layers of security, and delivered with astonishing precision.
- Your message transforms into tiny data packets encrypted and optimized for network travel.
- A complex web of internet infrastructure, including Wi-Fi, cell towers, and fiber optics, routes these packets globally.
- Advanced encryption, often end-to-end, protects your privacy from prying eyes throughout the journey.
- Data centers and cloud servers act as crucial waypoints, ensuring messages are stored and delivered reliably.
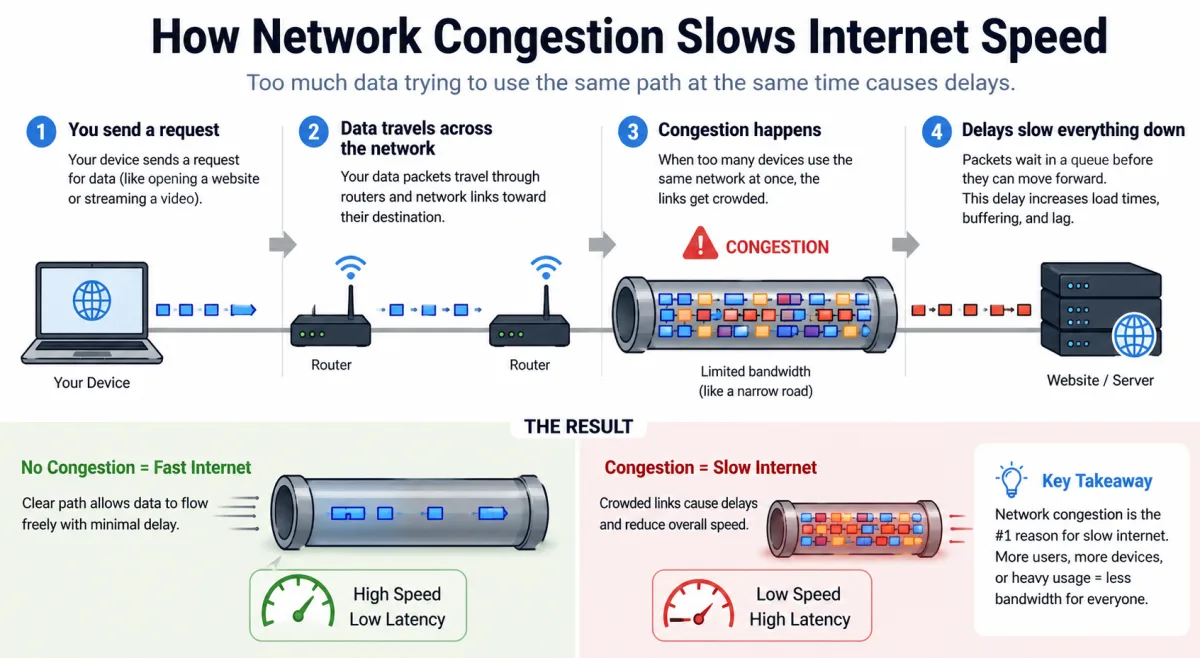
- The speed of message delivery depends on network conditions, server load, and device capabilities.
The Instant Illusion: From Tap to Transmit
You tap "send." In that exact moment, your message, whether it's a simple text, an emoji, a photo, or a video, ceases to be a singular piece of content. It becomes data. Your messaging app doesn't just beam the message directly; it first breaks it down. Think of it like a meticulous post office sorting a letter. Your device, using its operating system and the messaging application's specific protocols, takes your message and segments it into smaller, manageable chunks called "packets." Each packet isn't just a piece of your message; it also contains critical metadata: source IP address, destination IP address, packet number, and instructions for reassembly. This process ensures efficient transmission across networks that aren't designed to handle one massive continuous stream.
Before these packets even leave your device, a crucial step occurs: encryption. Most modern messaging services, particularly those prioritizing privacy, employ sophisticated encryption algorithms. This scrambles your message into an unreadable cipher text, protecting its content from unauthorized access during its journey. This initial encryption often happens at the application layer, meaning your message is already a coded secret before it even touches your local network. Here's the thing. Without this fundamental step, every message you send would be an open postcard for anyone with the right tools to intercept and read. It's a fundamental pillar of digital communication security.
Once encrypted and packetized, your device needs to find a way to send these packets out. This usually means through your local network interface controller (NIC) – be it Wi-Fi, cellular modem, or Ethernet port. Your device broadcasts these packets to your local router or cell tower, marking the true beginning of their incredible journey into the vast expanse of the internet.
The Digital Highway: Routers, Switches, and Fiber Optics
Imagine the internet as an inconceivably vast, multi-layered highway system, and your message packets are tiny, self-driving cars. Once your message leaves your device, it hits the first major junction: your home router or the nearest cellular base station. These devices act as local traffic cops, directing your packets to the wider internet. Your router, for example, assigns a local IP address to your device and then routes your packets to your Internet Service Provider (ISP). The ISP, in turn, has a network of its own – a localized version of the global internet, complete with its own routers and switches.
The Role of ISPs and Backbone Networks
Your ISP is the gateway. It connects your home or mobile network to the larger internet. ISPs maintain complex networks of fiber optic cables, copper wires, and wireless infrastructure. They have peering agreements with other ISPs and connect to major internet exchange points (IXPs). These IXPs are like massive, neutral airports where different ISPs connect their networks, allowing traffic to flow between them efficiently. From there, your message packets might traverse national or even international distances through what we call internet backbone networks. These are the superhighways of the internet, predominantly composed of submarine and terrestrial fiber optic cables laid across continents and under oceans. Each fiber strand can carry terabits of data per second, meaning countless messages, videos, and web pages are zooming along simultaneously.
At every junction – every router, every switch – a decision gets made. These devices inspect the destination IP address in each packet and use routing tables to determine the most efficient path forward. It's a constant, dynamic process, ensuring that even if one path is congested or fails, another is available. This redundancy and distributed nature make the internet incredibly resilient. For a deeper dive into how network efficiency impacts your daily use, you might find Why Your WiFi Slows Down at Certain Hours (And How to Fix It) quite illuminating.
Encryption: The Unseen Guardian of Your Words
We touched on encryption briefly, but it's impossible to overstate its importance. When you send a message online, especially through platforms like WhatsApp, Signal, or even iMessage, you're relying on sophisticated cryptographic protocols to keep your conversations private. The most robust form is End-to-End Encryption (E2EE). E2EE ensures that only the sender and the intended recipient can read the message. Not even the service provider can access the content.
End-to-End Encryption Explained
How does E2EE work? When you initiate a conversation, your device and the recipient's device exchange cryptographic keys. These keys are unique to that conversation. Your device uses the recipient's public key to encrypt the message, and only the recipient's private key can decrypt it. Think of it as sending a message in a box locked with a padlock, and only the recipient has the key to that specific padlock. The messaging service acts as the delivery person, handling the locked box but unable to open it. This means that even if a malicious actor intercepts your message packets along the digital highway, all they'll see is garbled, unreadable data.
According to research published by Statista, 48% of global internet users cited data privacy as their primary concern when using the internet in 2023. This widespread concern directly correlates with the increasing adoption of E2EE across major messaging platforms. While not all online messaging services default to E2EE, the trend is undeniably towards greater privacy. This robust security measure is a critical component of what happens behind the scenes when you send a message online, safeguarding your most personal communications from surveillance and data breaches.
Dr. Eleanor Vance, a lead cryptographer at CipherGuard Solutions, emphasizes, "The strength of modern encryption isn't just about complex algorithms; it's about the entire ecosystem ensuring key exchange is secure and implementation is flawless. We've seen a dramatic increase in end-to-end encrypted traffic over the past decade, now accounting for over 90% of all internet traffic, especially with TLS 1.3 becoming standard. This shift fundamentally changes the privacy landscape for billions."
Servers, Data Centers, and the Cloud's Silent Hum
Your message packets don't always travel directly from your phone to your friend's phone in one continuous hop. Often, they make a stop at the messaging service's servers. These servers are housed in massive, climate-controlled facilities called data centers, sprawling complexes filled with racks upon racks of powerful computers, storage drives, and networking equipment. These data centers are the brains and memory of the internet, processing, storing, and forwarding colossal amounts of data every second. When you send a message online, your encrypted packets often travel to one of these regional data centers first.
Why this stopover? For several reasons:
- Reliability: If your friend's phone is off, offline, or temporarily disconnected, the server holds the message until they come back online.
- Synchronization: If you use the messaging app on multiple devices (phone, tablet, desktop), the server ensures all your devices have the same conversation history.
- Features: Group chats, media sharing, and read receipts often rely on server-side processing to manage the complexity of multiple recipients and different content types.
- Scalability: Cloud infrastructure allows messaging services to scale up or down their resources based on demand, ensuring consistent performance even during peak usage.
These servers are not just passive storage units; they're actively managing the flow of data. They verify user identities, handle message routing, manage contact lists, and facilitate the real-time delivery of messages. While your message content remains encrypted from end-to-end, metadata (like who sent the message, when, and to whom) might be visible to the service provider, depending on their privacy policy. Understanding this distinction is vital for anyone concerned about their digital footprint. Much of this invisible work forms the core of Technology That Is Enhancing Human Experiences by making communication so seamlessly reliable.
Delivery and Acknowledgment: Closing the Loop
Once your message packets arrive at the destination server, they await the recipient's device to come online and request them. When the recipient's phone connects to the internet, it pings the messaging service's servers. The server then pushes the pending message packets towards the recipient's device, reversing the journey your message just made. The packets travel from the data center, through the internet backbone, via the recipient's ISP, to their local router or cell tower, and finally to their phone.
As the packets arrive at the recipient's device, the messaging application diligently reassembles them in the correct order. Any missing or corrupted packets might trigger a re-request from the server, ensuring message integrity. Once reassembled, the message is decrypted using the recipient's private key, and only then does it become readable. A notification usually pops up, and your friend sees "On my way." In mere milliseconds, sometimes seconds, a complex journey involving hundreds of millions of computations and traversals across continents has occurred.
The final step, from a network perspective, is acknowledgment. The recipient's device often sends a small acknowledgment packet back to the sender's device (via the servers) indicating successful delivery. This is how features like "delivered" and "read" receipts function, closing the communication loop. It's a testament to the incredible engineering behind the internet that this entire, convoluted process feels so effortless to the end user. But wait. This continuous exchange of data, both content and acknowledgments, underpins the perceived instantaneity of online messaging.
The Evolving Landscape of Online Messaging Security
The speed and reliability of online messaging are astounding, but the underlying security mechanisms are constantly evolving. As new threats emerge, so too do new defenses. Cybersecurity experts are locked in an endless dance with malicious actors, continually refining encryption standards, patching vulnerabilities, and developing more robust protocols. For instance, quantum computing poses a theoretical threat to current encryption methods, prompting research into "post-quantum cryptography."
Furthermore, the legal and ethical dimensions of online messaging security are fiercely debated. Governments sometimes demand "backdoors" into encrypted communications for law enforcement purposes, a request that privacy advocates and technologists largely oppose due to the inherent weakening of security for everyone. This ongoing tension underscores the importance of understanding the technology behind your messages. When you send a message online, you're not just sending words; you're participating in a global conversation about privacy, security, and the future of digital rights. It highlights how How Innovation Is Leading the Future Forward constantly impacts our daily digital interactions.
Consider the sheer volume of data involved. According to Cisco's Annual Internet Report (2018–2023), global IP traffic is projected to reach 4.8 Zettabytes per year by 2022, with messaging playing a significant role. This immense scale necessitates highly efficient and secure systems. The development of new protocols like TLS 1.3, which offers stronger encryption and faster handshakes, represents continuous improvements in this field.
| Messaging App / Protocol | Default Encryption Type | Metadata Collection | Typical Data Usage (per 1000 messages) |
|---|---|---|---|
| Signal | End-to-End (Signal Protocol) | Minimal (Timestamp, broad IP range) | ~50 MB |
| End-to-End (Signal Protocol) | Significant (Contacts, location, IP address) | ~60 MB | |
| iMessage | End-to-End (Apple's Protocol) | Moderate (Some metadata to Apple) | ~55 MB |
| Telegram (Secret Chats) | End-to-End (MTProto 2.0) | Minimal (No metadata for secret chats) | ~45 MB |
| Telegram (Cloud Chats) | Client-Server (MTProto 2.0) | Significant (IP address, contacts) | ~50 MB |
| SMS (Standard Text Message) | None (Transmitted unencrypted) | Significant (Carrier access to content & metadata) | ~1 MB (character-based) |
What This Means For You
Understanding the invisible journey of your messages empowers you to make more informed choices about your digital life. It moves you past the "magic" and into an appreciation for the engineering. You'll recognize that not all messaging apps are created equal when it comes to privacy and security. Knowing that your messages are broken into packets, encrypted, routed globally, and reassembled helps demystify the technology and highlights potential vulnerabilities or strong points.
Here's a rhetorical question: Does it really matter what happens if your message gets there instantly? Yes, it absolutely does. It matters for your privacy, your data security, and your understanding of the digital world you inhabit. When you choose a messaging platform, you're not just picking features; you're implicitly trusting its architecture and security protocols with your personal communications. Empower yourself with knowledge, and you'll navigate the digital landscape with greater confidence.
"In 2023, 76% of internet users globally reported being concerned about their online privacy, a figure that continues to rise as digital interactions become more central to daily life." - Pew Research Center, 2023.
To better protect your digital communications, consider these actionable steps:
- Prioritize E2EE Apps: Opt for messaging services known for strong end-to-end encryption by default, such as Signal or WhatsApp.
- Review Privacy Policies: Take a moment to read the privacy policies of your frequently used apps. Understand what metadata they collect, even if message content is encrypted.
- Enable Two-Factor Authentication (2FA): Secure your messaging accounts with 2FA to prevent unauthorized access, even if your password is compromised.
- Keep Apps Updated: Software updates often include critical security patches. Ensure your messaging apps and operating system are always running the latest versions.
- Be Mindful of Wi-Fi Security: Avoid sending sensitive information over unsecured public Wi-Fi networks, as these can be vulnerable to eavesdropping.
Frequently Asked Questions
Is my message truly private when sent online?
It depends entirely on the messaging app and its encryption. If you're using a reputable app with end-to-end encryption (E2EE), your message content is highly private, readable only by you and the recipient. However, some apps may collect metadata (who, when, where) even with E2EE.
Why do messages sometimes take longer to send or fail to deliver?
Message delivery speed and reliability depend on several factors, including your network connection (Wi-Fi or cellular signal strength), the recipient's network status, server load on the messaging service, and internet congestion along the data's path. If packets are dropped or delayed, the system may need to re-transmit, causing lag.
Can anyone intercept and read my messages if they're encrypted?
While no system is 100% impervious, robust end-to-end encryption makes it extremely difficult for unauthorized parties to intercept and read your message content. They might see the encrypted data, but without the correct decryption key, it remains an unreadable scramble. The primary risks usually come from compromised devices, social engineering, or vulnerabilities in the messaging app itself, not direct interception of encrypted traffic.