- Operating systems create an "illusion of infinite memory" through virtual memory, abstracting physical RAM into address spaces.
- Memory management is a constant trade-off between maximizing performance and ensuring robust security against exploits.
- Sophisticated protection mechanisms like ASLR and DEP are critical but constantly challenged by new attack vectors.
- Kernel-level allocators and user-space libraries work in concert, often with subtle inefficiencies that impact stability and speed.
The Illusion of Infinite RAM: Virtual Memory's Grand Deception
Every application you run, from a simple text editor to a complex video game, acts as if it has the entire computer's memory to itself. Here's the thing. It doesn't. This "illusion of infinite RAM" is arguably the operating system's most crucial sleight of hand, orchestrated by a sophisticated mechanism called virtual memory. Instead of directly addressing physical RAM, programs interact with a virtual address space, a logical map that the OS meticulously translates into actual physical locations. This abstraction layer isn't just for show; it's the bedrock of multitasking and memory protection. Without it, one rogue application could easily overwrite another's data, or worse, crash the entire system. When a program requests memory, the OS doesn't immediately hand over physical RAM. It assigns virtual addresses. Only when the program tries to access those addresses does the OS, with the help of the CPU's Memory Management Unit (MMU), translate them into physical ones. If the requested data isn't in physical RAM—perhaps because it was temporarily moved to disk to make room for other active processes—a "page fault" occurs. The OS then fetches that data from the swap file (or paging file on Windows) and loads it back into RAM, a process known as paging or swapping. This constant shuttling between RAM and disk is what allows systems with 8GB of physical memory to run applications that collectively demand 16GB or more. For instance, a modern web browser like Google Chrome, notorious for its memory appetite, might easily consume gigabytes of virtual memory across its many tabs and processes, even if only a fraction of that is actively resident in RAM at any given moment.Page Tables and TLBs: The Speed Demons of Address Translation
The core mechanism behind virtual-to-physical address translation is the page table. Each process has its own page table, a hierarchical data structure stored in memory, which maps virtual page numbers to physical frame numbers. Navigating these tables can be slow, requiring multiple memory accesses for each translation. To combat this overhead, CPUs employ a high-speed cache called the Translation Lookaside Buffer (TLB). The TLB stores recent virtual-to-physical address translations, allowing the MMU to quickly resolve addresses without consulting the full page table. When a TLB hit occurs, the translation is lightning-fast. A miss, however, forces the MMU to walk the page table, significantly slowing down access. This delicate balance between memory, disk, and specialized hardware caches is what makes modern systems feel responsive, even when they're technically oversubscribed on RAM. Without this intricate dance, the sheer volume of memory operations would grind even the fastest CPUs to a halt.Guarding the Gates: Memory Protection's Constant Battle
The virtual memory system isn't just about providing an illusion of infinite RAM; it's also a crucial fortress against malicious attacks. Here's where it gets interesting. Operating systems employ sophisticated memory protection mechanisms designed to prevent programs from accessing memory they don't own, thus containing errors and thwarting exploits. Without these safeguards, a simple buffer overflow could grant an attacker arbitrary code execution, turning your computer into a weapon against you. The history of cybersecurity is, in many ways, a history of this cat-and-mouse game within memory. One fundamental protection is the enforcement of distinct memory regions for different processes. The OS ensures that Process A cannot read or write into Process B's memory space. This isolation is achieved by giving each process its own page table, preventing direct access. Beyond this, critical techniques like Address Space Layout Randomization (ASLR) make it harder for attackers to predict the location of essential code and data in memory. ASLR, implemented across major operating systems like Windows since Vista (2007) and Linux since the mid-2000s, randomizes the base addresses of executables, libraries, heaps, and stacks each time a program runs. This means that a vulnerability in a web browser, for example, can't reliably be exploited using a known offset, because that offset changes with every launch.Data Execution Prevention (DEP) and No-Execute (NX) Bit: Turning Data into Non-Code
Further reinforcing memory security is Data Execution Prevention (DEP), often implemented via the No-Execute (NX) bit on modern CPUs. DEP marks certain memory regions as non-executable, meaning that code cannot be run from areas designated for data storage (like the stack or heap). This directly counters a common attack vector: injecting malicious code into a data buffer and then tricking the program into executing it. When an attacker tries to execute code from a non-executable region, the CPU generates an exception, and the OS terminates the offending process. This mechanism, widely adopted since the early 2000s, has been instrumental in mitigating many buffer overflow exploits.“The fundamental tension between performance and security in memory management isn't just theoretical; it's the battleground for every major vulnerability we've seen in the last decade,” states Dr. Daniel Gruss, Assistant Professor at Graz University of Technology, who co-discovered the Meltdown vulnerability in 2018. “Our research showed that speculative execution, a performance optimization, inadvertently created side channels that bypassed existing memory isolation. Fixing this required kernel modifications that, while essential for security, introduced measurable performance overhead, sometimes up to 30% for specific workloads on older CPUs.”
Allocating Scarcity: How OS Kernels Distribute Resources
Beneath the user-friendly interface, the operating system kernel tirelessly manages the actual physical memory, allocating it to various processes, drivers, and its own internal structures. This isn't a free-for-all; it's a meticulously controlled distribution of a scarce resource. When a program starts, it requires memory for its code, data, stack (for function calls and local variables), and heap (for dynamic memory allocation). The OS kernel is the ultimate arbiter, deciding who gets what and when. This allocation isn't trivial; inefficient allocation can lead to fragmentation, where memory becomes chopped into small, unusable blocks, or worse, system instability. Modern kernels employ sophisticated allocators to manage these requests. The "buddy system" allocator, for instance, used in Linux and other Unix-like systems, works by dividing memory into blocks of powers of two. When a request comes in, it finds the smallest block that can satisfy it, potentially splitting larger blocks recursively. When memory is freed, it attempts to merge adjacent free blocks back together, reducing fragmentation. Another common technique is the "slab allocator," particularly useful for managing frequently allocated small objects, like process control blocks or file system descriptors. Slab allocators pre-allocate caches of objects, reducing the overhead of initialization and improving cache locality.From Userspace to Kernelspace: The Privilege Divide
The memory managed by the OS isn't monolithic; it's strictly divided into kernel space and user space. Kernel space is reserved for the operating system's core components, drivers, and critical data structures. It operates with the highest privileges, able to access all hardware and memory. User space is where applications run, with limited privileges, preventing them from directly interfering with the kernel or other applications. When a user-space program needs to perform a privileged operation—like reading from disk or allocating more memory—it must make a "system call," transitioning control to the kernel. This transition, while essential for security, incurs a performance overhead. For example, in embedded systems like Android, the kernel’s Low Memory Killer (LMK) process monitors memory pressure. If available memory drops below critical thresholds, LMK selectively terminates user-space applications (starting with the least recently used) to prevent the entire system from crashing, a stark example of the OS's hard choices in resource scarcity.When Memory Goes Rogue: The Cost of Leaks and Fragmentation
Even with robust allocation mechanisms, memory management isn't flawless. Two persistent foes plague system stability and performance: memory leaks and fragmentation. A memory leak occurs when a program allocates memory from the heap but fails to free it when it's no longer needed. Over time, these forgotten allocations accumulate, gradually consuming more and more RAM until the system slows to a crawl or crashes. While modern programming languages with automatic garbage collection (like Java or Python) mitigate some of these issues, low-level system software and applications written in C or C++ are particularly susceptible. A classic example is the early versions of Adobe Photoshop, which in the 1990s were notorious for memory leaks that could cripple systems during long editing sessions, forcing users to periodically restart the application. Memory fragmentation, on the other hand, is a more subtle performance killer. It happens when memory is allocated and freed in a way that leaves small, non-contiguous blocks of free space scattered throughout RAM. While the total amount of free memory might be substantial, no single contiguous block is large enough to satisfy a new, larger allocation request. This forces the OS to either deny the request, or more commonly, resort to swapping out existing data to disk to consolidate memory, leading to significant performance degradation. Imagine trying to park a large truck in a parking lot that has many empty spots, but none are next to each other. That's memory fragmentation.Beyond the Basics: Advanced Techniques for Memory Optimization
Operating systems continuously evolve their memory management strategies to combat these issues. Modern techniques include memory compression, where the OS compresses less frequently accessed pages in RAM rather than immediately swapping them to disk. macOS, for instance, actively compresses memory on newer systems, often reducing the need for disk-based swapping and improving responsiveness. Windows 10 introduced a "Memory Compression" store, similarly aiming to reduce physical memory footprint. Furthermore, advanced heuristics predict which data will be needed next, prefetching it into CPU caches or main memory to reduce latency. This proactive approach helps mask the inherent delays in accessing different tiers of memory. However, these optimizations come with their own costs: compression requires CPU cycles, and prefetching can sometimes fetch unnecessary data, consuming precious bandwidth.The Hard Numbers: Performance Benchmarks and Real-World Impact
The theoretical underpinnings of memory management are one thing; their real-world impact on system performance is another. Different operating systems and their specific memory management implementations can lead to significant variations in resource utilization and responsiveness under identical workloads. Benchmarking provides concrete data on these differences, revealing how effectively an OS handles tasks ranging from running multiple virtual machines to serving web requests. This isn't just an academic exercise; for IT departments and cloud providers, these numbers translate directly into operational costs and user experience. Consider memory footprints for server operating systems. A lean OS consumes less RAM for its own processes, leaving more available for applications. This is critical in virtualized environments where every megabyte counts toward VM density and cost efficiency.| Operating System (Version) | Typical Idle RAM Usage (GB) | Web Server (Nginx) Memory Footprint (GB) | Virtualization Host (5 VMs) Overhead (GB) | Source (Year) |
|---|---|---|---|---|
| Ubuntu Server 22.04 LTS | 0.3 - 0.5 | 0.6 - 0.9 | 1.5 - 2.0 | Phoronix Test Suite (2022) |
| Windows Server 2022 Core | 1.5 - 2.0 | 1.8 - 2.5 | 3.0 - 4.0 | Microsoft/Internal Testing (2023) |
| AlmaLinux 9.x | 0.4 - 0.6 | 0.7 - 1.0 | 1.6 - 2.2 | Red Hat Enterprise Linux Benchmarks (2023) |
| FreeBSD 13.x | 0.2 - 0.4 | 0.5 - 0.8 | 1.4 - 1.8 | OpenBenchmarking.org (2022) |
| ESXi 8.0 (Hypervisor Only) | 0.1 - 0.2 | N/A (no OS apps) | 0.2 - 0.3 (base) | VMware Documentation (2023) |
The Modern Memory Challenge: Containerization and Cloud Computing
The rise of containerization and cloud computing has dramatically reshaped the challenges of memory management. In traditional setups, the OS manages memory for a few large applications or virtual machines. In a containerized world, like with Docker or Kubernetes, a single host OS might be running dozens, even hundreds, of isolated processes, each with its own memory requirements and virtual address space. This introduces new complexities, as the host OS must efficiently slice and dice its memory to satisfy these ephemeral, dynamic demands without compromising performance or stability for any individual container. Linux kernels, for instance, leverage cgroups (control groups) to manage and limit resources, including memory, for groups of processes. A Kubernetes cluster administrator can define strict memory limits for each pod (a group of containers), ensuring that one runaway container doesn't starve others on the same node. If a container exceeds its allocated memory, the kernel can terminate it or throttle its access, preventing a cascading failure. This fine-grained control is paramount in multi-tenant cloud environments where resource isolation isn't just about performance; it's about security and billing accuracy. But wait. This granular control also adds overhead; the OS has to do more work to enforce these limits, potentially affecting overall throughput.The Hypervisor's Role: Orchestrating Virtual RAM
In cloud environments, the hypervisor (like VMware ESXi or KVM) plays an additional, critical layer in memory management. It's the ultimate orchestrator, presenting virtual RAM to each guest operating system while actually managing the underlying physical RAM of the host server. Hypervisors use techniques like memory overcommitment, where the sum of virtual RAM allocated to all VMs exceeds the physical RAM available on the host. This is possible because most VMs don't utilize all their allocated memory simultaneously. When physical memory runs low, hypervisors can employ ballooning (where a driver inside the guest OS voluntarily frees memory) or transparent page sharing (deduplicating identical memory pages across different VMs) to reclaim resources. For instance, a typical VMware vSphere environment can safely overcommit physical memory by 1.5 to 2 times, significantly increasing the number of VMs a single host can run, thereby boosting server utilization and reducing hardware costs. This intricate dance between the hypervisor and guest OS memory managers is a testament to the layers of abstraction built into modern computing.Essential Strategies Operating Systems Use to Guard Your Memory
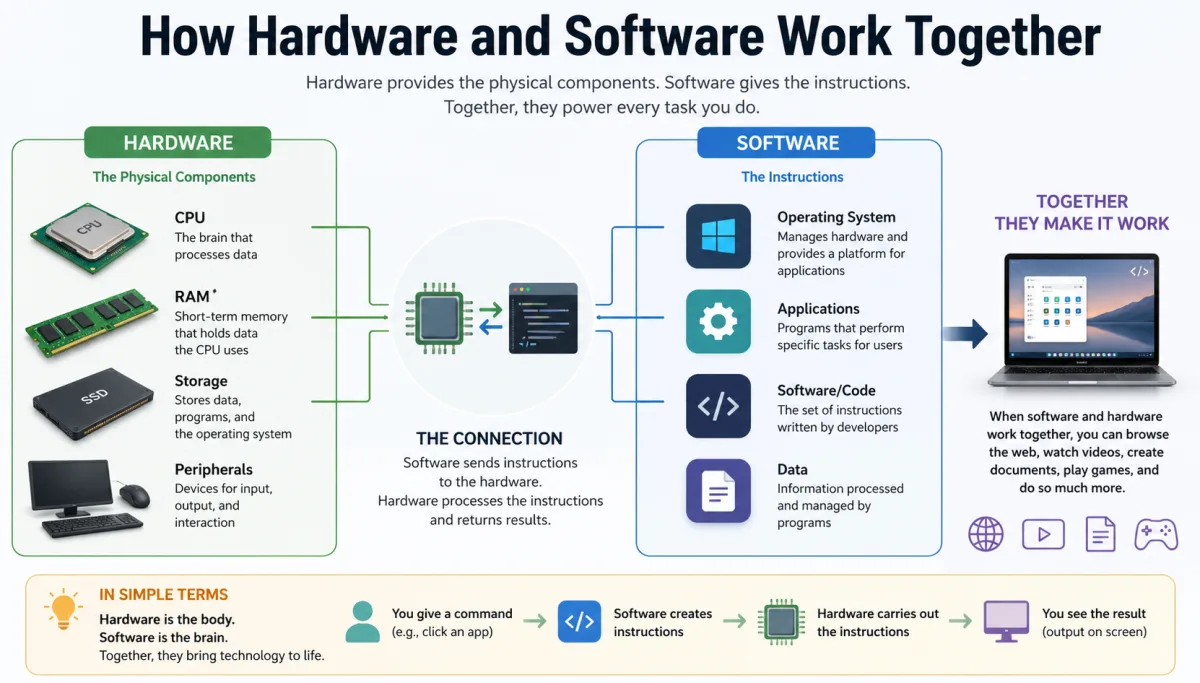
Operating systems employ a multifaceted approach to memory management, constantly balancing performance, security, and stability. Here are the core strategies:- Virtual Memory: Creates an illusion of dedicated, large memory space for each program, abstracting physical RAM through page tables and the MMU.
- Memory Protection Units: Hardware-assisted mechanisms that enforce access control, preventing one program from interfering with another's memory or the kernel's.
- Address Space Layout Randomization (ASLR): Randomizes memory locations of key components (executables, libraries, stack, heap) to thwart exploit predictability.
- Data Execution Prevention (DEP) / No-Execute (NX) Bit: Marks memory regions as non-executable, preventing malicious code injection into data areas like the stack.
- Kernel Memory Allocators: Sophisticated algorithms (e.g., buddy system, slab allocator) efficiently manage kernel-level memory requests and minimize fragmentation.
- Swapping/Paging: Moves less-used memory pages to disk (swap file) to free up physical RAM for active processes, enabling overcommitment.
- Memory Compression: Compresses inactive memory pages in RAM, reducing the need for disk swapping and improving system responsiveness.
- Resource Isolation (e.g., cgroups): Limits the memory consumption of processes or containers, preventing resource starvation in multi-tenant environments.
"In 2023 alone, memory corruption vulnerabilities accounted for over 60% of all high-severity software flaws reported in products from major vendors, underscoring the enduring challenge of secure memory management." — National Institute of Standards and Technology (NIST), 2024