In November 2021, a sophisticated ransomware attack crippled systems at Kronos Private Cloud, a major provider of workforce management solutions. The fallout wasn’t just about disrupted payrolls; it exposed a deeper truth about the infrastructure powering much of our digital world: the virtual machine. While the precise attack vector remains complex, the incident underscored a critical vulnerability often downplayed in the popular narrative of virtualization: the hypervisor, the very software layer that makes running different operating systems on one device possible, is itself a prime target. Here's the thing. We laud virtual machines for their efficiency and isolation, but this "magic" isn't a simple act of digital partition; it's a meticulously engineered illusion of separation, one that carries inherent performance overheads and, more crucially, opens subtle but significant security risks by sharing physical hardware.
- Virtual machine isolation is a software abstraction, not absolute physical separation, leading to shared resource contention.
- The hypervisor, the core of virtualization, is a single point of failure and a high-value target for sophisticated cyberattacks.
- Performance overhead isn't just about CPU cycles; it encompasses memory, storage I/O, and network, significantly impacting application responsiveness.
- Many organizations unknowingly perpetuate critical vulnerabilities by virtualizing outdated, insecure legacy operating systems without adequate security measures.
The Hypervisor: Orchestrating the Illusion of Independence
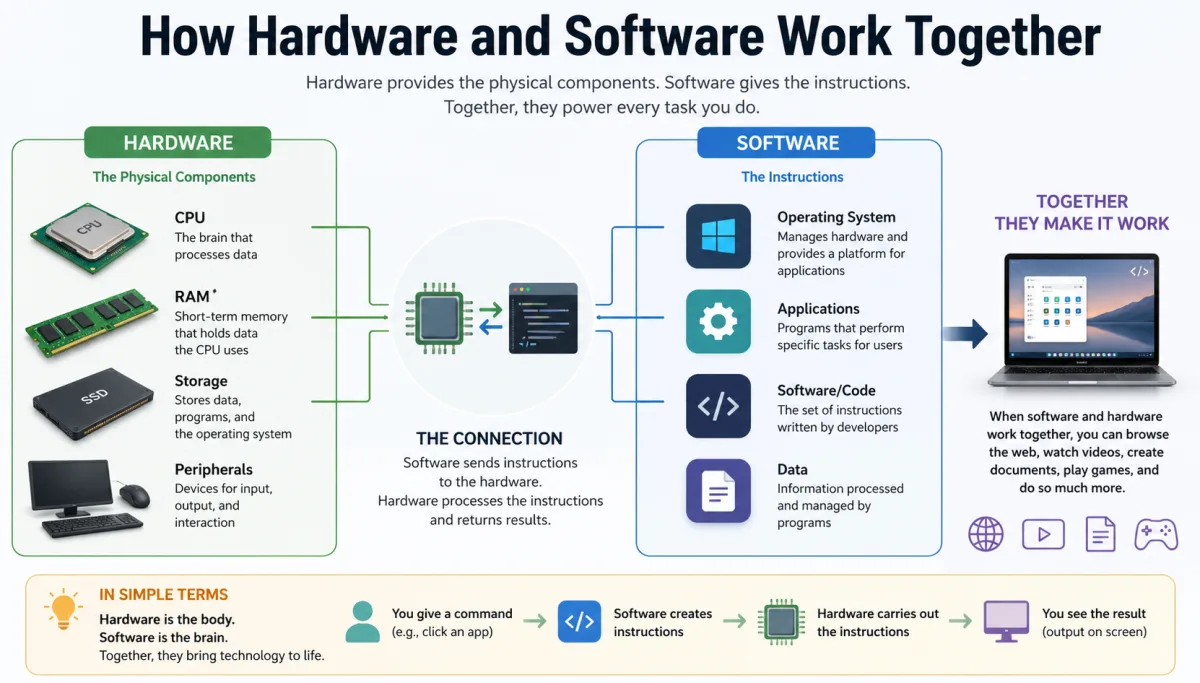
At its core, understanding how virtual machines run different OS on one device means grappling with the hypervisor. This isn't just a piece of software; it's a powerful arbiter, a manager of managers, that sits directly on the physical hardware (Type 1, or "bare-metal" hypervisor like VMware ESXi or Microsoft Hyper-V) or runs as an application within a host operating system (Type 2, like Oracle VirtualBox or VMware Workstation). Its job is deceptively simple: to create, manage, and mediate access to the underlying hardware for multiple, isolated virtual environments, each running its own operating system—a "guest OS." It presents each guest OS with a virtualized version of the hardware it expects to see: virtual CPUs, virtual memory, virtual network interfaces, and virtual disks. The guest OS then believes it has exclusive access to these resources, oblivious to the fact that it's sharing the actual physical components with other guests.
Consider a large enterprise like Goldman Sachs, which uses extensive virtualization to run thousands of applications across its data centers. They aren't just saving on hardware; they're creating isolated environments for different financial services, ensuring that a bug in one application doesn't bring down another. The hypervisor makes this possible by intercepting calls from the guest OS that would normally go directly to hardware. It translates these calls, allocates physical resources, and then passes the results back to the guest. This process, known as "trap-and-emulate" or "binary translation," creates the necessary illusion of dedicated hardware. Modern CPUs, like Intel's VT-x or AMD's AMD-V, include hardware-assisted virtualization features that significantly speed up this process, allowing the guest OS to execute many instructions directly on the CPU without hypervisor intervention. This hardware assist is crucial; without it, the performance penalty would be far too great for most enterprise applications.
But wait. This intricate dance means the hypervisor isn't just a mediator; it's a gatekeeper, a single point of control for all virtualized environments. Its integrity is paramount, making it a prime target for anyone looking to gain control over an entire server's worth of virtual machines.
The Illusion of Isolation: Shared Resources and Hidden Vulnerabilities
While virtual machines are celebrated for their isolation, the reality is more nuanced. They don't exist in a vacuum; they share the same physical CPU, memory, network interfaces, and storage. This shared reality, while incredibly efficient, is also the source of subtle yet potent vulnerabilities and performance contention. The hypervisor strives to create a secure boundary, but the very act of sharing physical components inevitably leaves traces, which malicious actors can exploit.
Side-Channel Attacks: When Shared Caches Leak Secrets
One of the most insidious vulnerabilities arises from side-channel attacks. These don't directly exploit software bugs but rather capitalize on the observable physical effects of computations. A prime example is the exploitation of shared CPU caches. When two virtual machines run on the same physical processor core, they might share the same L1 or L2 cache. An attacker in one VM can monitor the cache access patterns of another VM – perhaps a VM handling sensitive cryptographic operations. By precisely timing how long it takes for certain data to be accessed, they can infer information about the cryptographic key being used. The 2018 Spectre and Meltdown vulnerabilities, affecting nearly every modern CPU, starkly highlighted how speculative execution and shared caches could be weaponized to bypass isolation boundaries, even those enforced by hypervisors. Researchers at Graz University of Technology demonstrated that these vulnerabilities could allow data leakage between VMs, fundamentally challenging the notion of complete software isolation.
The Hypervisor as the Ultimate Target: A Single Point of Failure
The hypervisor sits at the lowest layer of the software stack, directly above the hardware. This privileged position makes it an incredibly attractive target. A successful attack on the hypervisor, often termed a "hyper-jacking" attack, grants an attacker control over all guest virtual machines running on that physical host. This isn't theoretical; it's a documented risk. In 2023, VMware released multiple critical security patches for its ESXi hypervisor, addressing vulnerabilities that could allow remote code execution or privilege escalation. An attacker exploiting such a flaw could essentially own an entire server farm, bypassing all the security measures implemented within individual guest operating systems. The National Institute of Standards and Technology (NIST) consistently highlights hypervisor security as a critical concern in its publications, recognizing its foundational role in cloud security.
Dr. Joanna Rutkowska, CEO of Gynvael Coldwind's Security Services, stated in a 2019 interview, "The hypervisor is the new kernel. If you compromise the hypervisor, you own everything above it. We've seen a shift from OS kernel exploits to hypervisor exploits as the ultimate prize for attackers." Her work on Blue Pill, a proof-of-concept hypervisor rootkit, demonstrated this vulnerability years ago, showing how a malicious hypervisor could effectively hide itself and control a guest OS without detection.
Performance: The Cost of Virtual Abstraction
While virtualization offers incredible flexibility, it’s not without its performance costs. The hypervisor, by design, introduces a layer of abstraction between the guest OS and the physical hardware. This translation and mediation process consumes CPU cycles, memory, and I/O bandwidth, leading to a phenomenon known as "virtualization overhead." For many common workloads, this overhead is negligible, particularly with modern hardware-assisted virtualization. However, for performance-sensitive applications, the cumulative effect can be significant, directly impacting user experience and operational efficiency.
CPU Scheduling and Memory Management Contention
When multiple virtual machines demand CPU cycles, the hypervisor must act as a scheduler, allocating slices of the physical CPU to each guest. This scheduling itself consumes resources. If too many demanding VMs are "oversubscribed" on a single physical host – meaning the combined virtual CPU cores exceed the physical cores – then each VM will experience performance degradation. Similarly, memory management is complex. While memory pages can be shared (e.g., if multiple VMs run the same OS kernel), the hypervisor still needs to map virtual memory addresses to physical ones. Techniques like "memory ballooning" or "transparent page sharing" help optimize memory usage, but they also add complexity and can introduce latency, particularly during peak loads. For example, a financial trading platform requiring sub-millisecond latency for transactions wouldn't tolerate the slight, unpredictable delays introduced by aggressive memory overcommitment.
I/O Bottlenecks: Virtual Disks, Real Delays
Perhaps the most significant performance bottleneck in many virtualized environments is I/O – specifically, disk and network I/O. When a guest OS wants to read or write to its virtual disk, that request must traverse the hypervisor layer, be translated, sent to the physical storage controller, and then the data returned through the same path. This adds latency. For applications heavily reliant on disk access, such as databases or large data analytics platforms, this can cripple performance. A study by Kroll (2022) revealed that I/O performance was a top three concern for 68% of IT managers deploying virtualized databases. While technologies like paravirtualized drivers (where the guest OS is aware it's virtualized and can communicate more efficiently with the hypervisor for I/O operations) significantly mitigate this, they don't eliminate the overhead entirely. Organizations using massive SAN (Storage Area Network) arrays, like CERN for its particle physics data, must carefully design their virtualized storage architecture to avoid these bottlenecks, often dedicating specific physical disks or network interfaces to high-performance VMs.
Virtualization's Unseen Footprint: Cloud, Containers, and Beyond
Virtualization isn't just for enterprise data centers anymore; its principles underpin much of the modern digital landscape. The entire cloud computing industry, from Amazon Web Services (AWS) EC2 instances to Google Cloud Platform's Compute Engine, is built on massive farms of physical servers running hypervisors that provision virtual machines on demand. When you spin up a server in the cloud, you're requesting a slice of a physical machine, managed by a hypervisor. This has democratized access to computing resources, allowing startups to scale globally without owning a single server.
However, the concept has evolved. While VMs provide strong isolation by encapsulating an entire operating system, a newer technology, containers (like Docker or Kubernetes), takes a different approach. Containers share the host OS kernel but provide isolation at the application layer. They're lighter, faster to start, and consume fewer resources than traditional VMs. But, here's where it gets interesting: many containerized applications still run within virtual machines in cloud environments. AWS Fargate, for instance, runs containers without requiring you to provision VMs directly, but underneath, it's still leveraging a highly optimized virtualized infrastructure to provide the necessary security and resource isolation. This hybrid approach demonstrates that the fundamental principles of virtual machines—resource abstraction and isolation—remain central, even as new technologies emerge to build upon them. The core need to run different operating systems or execution environments on one device, efficiently and securely, continues to drive innovation in this space.
The Legacy Trap: Virtualizing Vulnerabilities, Not Solving Them
One of the most compelling reasons for organizations to use virtual machines is to keep legacy applications alive. These applications, often critical to business operations, may only run on outdated operating systems like Windows Server 2003 or even ancient versions of Linux. Rather than undertaking costly and risky rewrites, companies simply virtualize these old systems. This "lift and shift" approach seems like a quick win: the application continues to function, and it's supposedly isolated within its VM.
But the conventional wisdom gets this wrong. Virtualizing a legacy system doesn't make it secure. It merely moves an insecure operating system from a physical server to a virtual one. These guest OSes often have unpatched vulnerabilities, known exploits, and lack modern security features. While the hypervisor provides a layer of isolation, it's not a magic bullet. If an attacker gains access to the legacy VM, they can still exploit its internal weaknesses, potentially using it as a beachhead to pivot to other systems on the network. A 2024 report by Mandiant noted that legacy systems, many running in virtualized environments, were implicated in over 20% of observed ransomware incidents, often serving as initial access points.
Take, for example, a major healthcare provider in the Midwest that virtualized an old patient records system running on Windows XP for cost savings. Despite network segmentation efforts, a zero-day exploit targeting an unpatched vulnerability within that Windows XP instance allowed an attacker to establish a foothold. From there, they launched a sophisticated lateral movement campaign, eventually compromising more secure systems. The VM didn't protect the legacy OS; it merely contained it, allowing its inherent insecurity to persist. This perpetuates a dangerous "legacy trap," where the perceived benefits of virtualization mask the underlying, unaddressed security debt.
Securing the Invisible Layer: Best Practices for Robust VM Environments
Given the complexities and potential vulnerabilities of virtualized environments, robust security isn't an afterthought; it's foundational. It's not enough to secure the guest operating systems; the hypervisor layer, the host hardware, and the entire virtualized network fabric demand vigilant attention. Here's what intelligent organizations are doing:
Securing virtualized environments requires a multi-layered approach that acknowledges the shared nature of the underlying hardware. Ignoring the hypervisor or believing that simply putting an old OS in a VM makes it secure is a dangerous miscalculation.
How to Harden Your Virtual Machine Environment Against Threats
- Patch Hypervisors Diligently: Treat hypervisor updates (e.g., for VMware ESXi, Microsoft Hyper-V, KVM) with extreme urgency. These patches often address critical vulnerabilities that could compromise all guest VMs.
- Implement Principle of Least Privilege: Limit administrative access to the hypervisor and management interfaces. Use strong, multi-factor authentication for all management accounts.
- Segment Virtual Networks: Use virtual LANs (VLANs) or network segmentation within your virtualized environment to isolate sensitive VMs from less secure ones. This limits lateral movement for attackers.
- Monitor Hypervisor Activity: Deploy specialized monitoring tools that can detect unusual activity on the hypervisor itself, not just within the guest OSes. Look for unauthorized changes or resource spikes.
- Harden Host Hardware: Ensure the physical host servers running your hypervisors are physically secure and that their firmware is regularly updated to protect against hardware-level exploits.
- Regularly Audit VM Configurations: Periodically review the security settings, network configurations, and resource allocations for each virtual machine to ensure they meet security baselines.
- Avoid Oversubscription of Resources: While efficient, excessive oversubscription of CPU, memory, or I/O can create performance issues that might be mistaken for attacks, or worse, mask real attack-related resource spikes.
"By 2025, over 75% of organizations will have experienced a multi-stage cyberattack originating from or involving a virtualized environment, up from less than 20% in 2020." - Gartner, 2023.
Beyond the Server Room: VMs in Everyday Tech and Development
The reach of virtual machines extends far beyond enterprise data centers and cloud platforms. They play a crucial, often unseen, role in development, testing, and even everyday consumer technology. Developers regularly use VMs to create isolated "sandboxes" for testing new software or replicating specific user environments. A software engineer at Google, for instance, might spin up a VM running an obscure Linux distribution to test a compiler's compatibility without needing to reconfigure their primary workstation. This agility drastically reduces development cycles and prevents "it works on my machine" syndrome.
For cybersecurity professionals, VMs are indispensable for malware analysis and penetration testing. Security researchers use VMs to safely detonate malicious software, observing its behavior without risking their host system. If a piece of ransomware encrypts a virtual disk, it's easily discarded and reset. This capability is critical for firms like CrowdStrike, which analyze millions of malware samples annually in controlled virtualized environments. Beyond this, even some consumer-grade operating systems, like Windows 10/11 Pro, offer Hyper-V, allowing users to run another OS for specific applications or testing without requiring a second physical computer. Furthermore, virtual machines are crucial for educational institutions and training programs, providing students with safe, reproducible environments to learn about operating systems, networking, and software development without fear of damaging shared resources. They're also integral to how modern operating systems handle some legacy applications, sometimes creating a virtualized environment on the fly to ensure compatibility with older software. This pervasive utility underscores their fundamental importance, even as the intricacies of their operation remain largely hidden from the average user.
| Hypervisor Type | Deployment | Resource Overhead (Typical) | Primary Use Case | Security Model | Example Products |
|---|---|---|---|---|---|
| Type 1 (Bare-Metal) | Directly on hardware | Low (1-5% CPU, 5-10% RAM) | Enterprise Data Centers, Cloud | Strong isolation, smaller attack surface | VMware ESXi, Microsoft Hyper-V, KVM, Xen |
| Type 2 (Hosted) | As an application on host OS | Moderate (5-15% CPU, 10-20% RAM) | Desktop Virtualization, Development, Testing | Relies on host OS security, larger attack surface | Oracle VirtualBox, VMware Workstation, Parallels Desktop |
| Container Runtime | Shares host OS kernel | Very Low (<1% CPU, <5% RAM) | Application Deployment, Microservices | Process isolation, less secure than VMs | Docker, containerd, Podman |
| OS-level Virtualization | Shares host OS kernel | Very Low (<1% CPU, <5% RAM) | Legacy Systems on same OS, Development | Process isolation, less secure than VMs | FreeBSD Jails, Linux LXC |
| Nested Virtualization | Hypervisor inside a VM | High (10-25% CPU, 15-30% RAM) | Testing, Cloud-within-Cloud | Complex, adds layers of vulnerability | ESXi on ESXi, Hyper-V on Hyper-V |
The evidence is clear: virtual machines are an indispensable technology, but their operational model fundamentally challenges the notion of absolute isolation. The hypervisor, while incredibly efficient, introduces a critical layer that can be a source of both performance bottlenecks and significant security vulnerabilities if not managed with extreme diligence. The prevalent practice of virtualizing insecure legacy systems without upgrading their internal security posture is not a solution but a dangerous deferral of risk. The data indicates that a substantial number of cyber incidents leverage weaknesses in virtualized environments, demanding a proactive, hypervisor-centric security strategy rather than a reactive, guest-OS-focused one. It’s not just about running different OS; it’s about managing the invisible, shared infrastructure that makes it happen.
What This Means For You
Understanding the true mechanics and hidden costs of how virtual machines run different OS on one device has direct implications for anyone working with modern computing infrastructure:
- For IT Professionals: You can't secure your network by only focusing on guest OS security. Your hypervisors are your first line of defense and a prime target. Prioritize hypervisor patching, robust access controls, and dedicated monitoring for the virtualization layer. Investigate solutions that enhance hypervisor-level security, like trusted platform modules (TPMs) and secure boot for your host hardware.
- For Developers: Performance isn't free. Be mindful of I/O-intensive operations and CPU demands when designing applications for virtualized environments. While containers offer efficiency, remember that they often run on VMs, meaning the underlying hypervisor still matters for security and resource availability. Consider optimizing your code for paravirtualized drivers where applicable.
- For Business Leaders: The "legacy trap" is a real, measurable risk. Virtualizing outdated systems provides convenience but can expose your entire infrastructure to significant cyber threats. Budget for modernization or invest heavily in advanced segmentation and monitoring specifically for these legacy virtualized assets. Recognize that a virtualized environment doesn't magically secure an insecure application.
- For Cloud Users: While cloud providers manage the underlying hypervisors, understanding their shared-resource nature helps you make informed choices about instance types and security groups. Don't assume cloud isolation is absolute; always implement robust security within your cloud-based VMs.
Frequently Asked Questions
What's the fundamental difference between Type 1 and Type 2 hypervisors?
Type 1 hypervisors (like VMware ESXi) run directly on the physical hardware, offering superior performance and security due to their minimal footprint and direct hardware access. Type 2 hypervisors (like VirtualBox) run as an application on top of a host operating system, making them easier to install but introducing more overhead and potential security dependencies on the host OS.
Can a virus in one virtual machine spread to another VM on the same host?
Direct spread through the hypervisor is rare but possible if the hypervisor itself is compromised. More commonly, a virus might spread if the virtual machines share a network and the guest OSes have vulnerabilities, or if shared folders are misconfigured. Effective network segmentation (e.g., using virtual LANs) helps contain such threats, and a 2023 study by Check Point found that 78% of VM-to-VM lateral movement attempts could be blocked by robust network micro-segmentation.
Does virtualization always make systems slower than running on bare metal?
Not always significantly, especially with modern hardware-assisted virtualization. For many typical workloads, the performance overhead is minimal (often less than 5%). However, for extremely I/O-intensive applications, real-time systems, or highly CPU-bound tasks, there can be a measurable performance difference due to the hypervisor's resource arbitration and translation layers. For instance, high-frequency trading platforms often opt for bare-metal servers to avoid any virtualization latency.
Are containers (like Docker) just a type of virtual machine?
No, they're distinct. Virtual machines encapsulate an entire operating system, providing strong isolation by virtualizing hardware. Containers share the host operating system's kernel but isolate applications and their dependencies at the process level. They are lighter and faster to deploy but offer less isolation than a full VM. Think of a VM as a separate house, and a container as an apartment in a shared building.